LATEST ARTICLES
Table of ContentsIntroduction
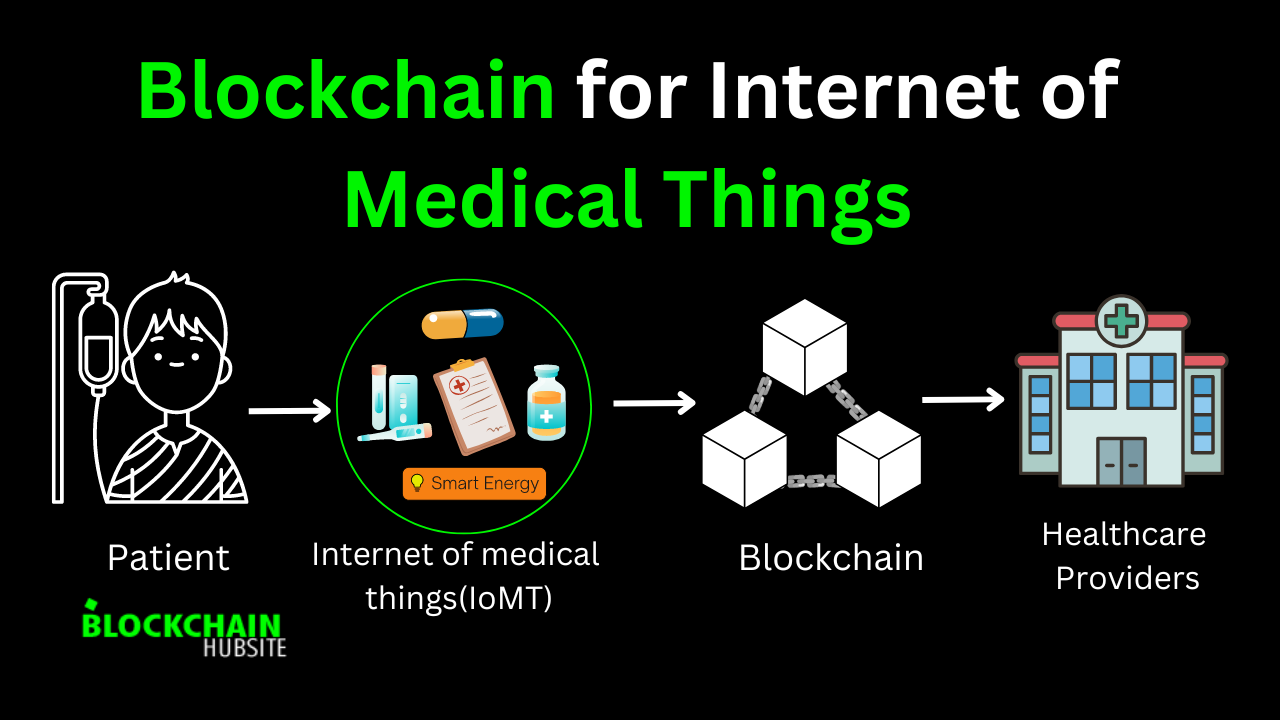
The Internet of Medical Things
Distributed Ledger Technology and Blockchain
Benefits...
Introduction
Blockchain Basics in Healthcare
Use Case 1: Securing Electronic Health Records (EHRs)
Use...
Understanding Blockchain Infrastructure and Functionality
Blockchain’s Transformative Impact on...
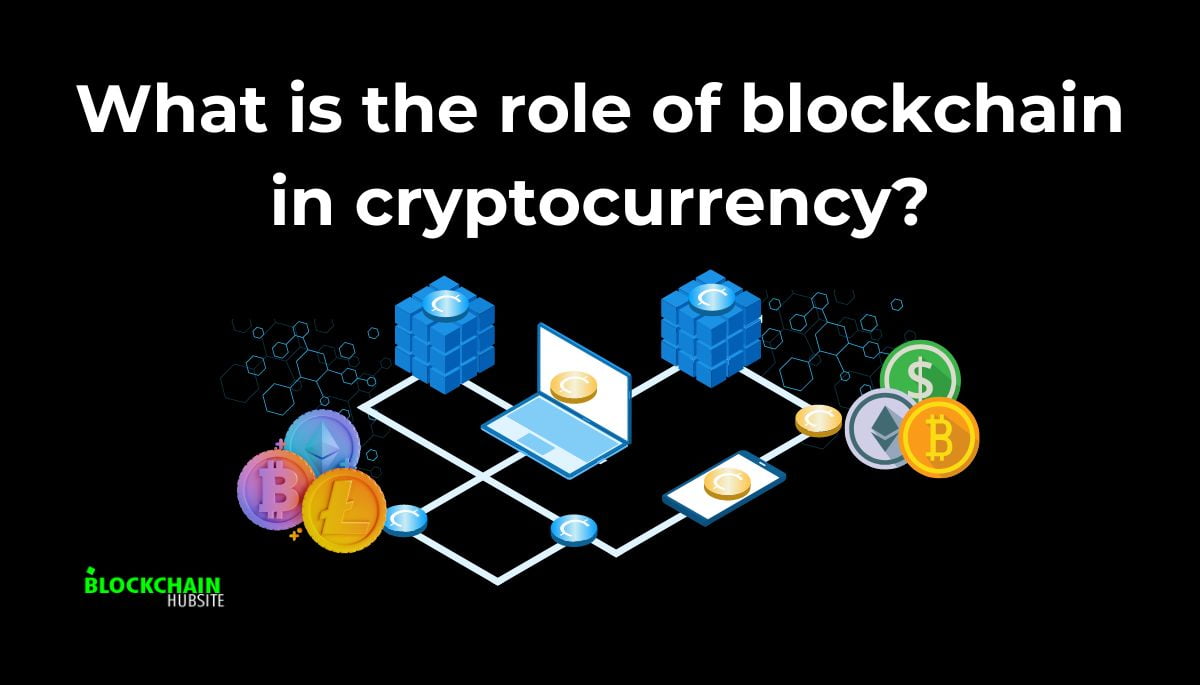
The Birth of Cryptocurrency
Blockchain Technology and Cryptocurrencies Explained
Role of Blockchain...
Realizing the Security Potential
Challenges in Securing Sensitive DataThe Rising Costs of Data Breaches
Vulnerabilities...
Building Trust Through Verified Identities
Fostering Financial IntegrityNavigating Decentralisation...
Introduction
DDoS Attack VectorsVolumetric attacks
Protocol Attacks
Application Layer AttacksDetection...
Introduction to tokenization of assetsDefinition of Asset Tokenization
Benefits such as enhanced liquidity,...
Introduction
5 Hidden and Rarely-Discussed Security Threats of Blockchain1. Illicit Asset Transfers
2....
IntroductionBlockchain Solves the Intellectual Property Problem of AI – as artificial intelligence...
Introduction
The Benefits of Blockchain for esports industryImproved Security and Fraud Prevention
Verifiable...
IntroductionOne of the most revolutionary and disruptive inventions of our time is blockchain technology,...